Global CyberSecurity
What Is a Keylogger?
Post Views: 916 Welcome to the world of keyloggers, where every keystroke you make may be watched, recorded, and potentially used against you! ...
Global CyberSecurity
WordPress 6.2.1 Security & Maintenance Release
Post Views: 878 On May 16, 2023, the WordPress core team released a crucial update — WordPress 6.2.1. This latest security and maintenance ...
Global CyberSecurity
Vulnerability in Essential Addons for Elementor Leads to Mass Infection
Post Views: 903 On May 11th, 2023, the very popular WordPress plugin Essential Addons for Elementor released a patch for a critical privilege ...
Global CyberSecurity
Websites Defaced with Belarusian Bottled Water Company Content
Post Views: 887 It’s not often that we get the opportunity to write about website defacements on this blog. Defacements — where a ...
Global CyberSecurity
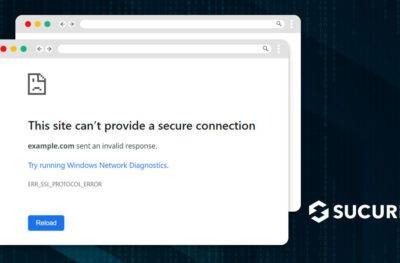
Troubleshooting ERR_SSL_PROTOCOL_ERROR: How to Fix this Pesky Error in 6 Steps
Post Views: 929 As a website owner (and frequent website visitor), you might have encountered the notorious ERR_SSL_PROTOCOL_ERROR at least once. This Secure ...
Global CyberSecurity
Xjquery Wave of WordPress SocGholish Injections
Post Views: 900 In November, 2022, my colleague Ben Martin described how hackers were using zipped files and encrypted WordPress options stored in ...
Global CyberSecurity
What is XML-RPC? Security Risks & How to Disable
Post Views: 920 XML-RPC is a protocol designed for WordPress to standardize communication between different systems, allowing external applications (such as other blogging ...